Tactical Analysis Of 60 Nation State Actors and 50 Ransomware Groups
The Azure cyber threat landscape has shifted from opportunistic incidents to highly coordinated campaigns. During the Microsoft fiscal year 2025 (July 1, 2024 – June 30, 2025), Microsoft actively tracked over: 60 nation-state actors, 50 ransomware groups, 368 access brokers operating globally within the same year. We reviewed and analyzed Microsoft’s findings, technical writings and recommendations and here’s what we found.
The Azure cyber threat landscape has shifted from opportunistic incidents to highly coordinated campaigns. During the Microsoft fiscal year 2025 (July 1, 2024 – June 30, 2025), Microsoft actively tracked over:
- 60 nation-state actors
- 50 ransomware groups, and hundreds of other criminal attackers
- 368 access brokers operating globally within the same year
We reviewed and analyzed Microsoft’s findings, technical writings and recommendations and here’s what we found.
Top Tactics: The Shift to "Logging In"
Modern adversaries are no longer just breaking in; they are increasingly "logging in" by exploiting Azure identities and cloud infrastructure.
Here are the top tactics they’re using.
- Password Spray Attacks: These remain the dominant identity attack vector, accounting for 97% of identity-based attempts. High-volume campaigns often utilize residential proxy networks to bypass traditional IP reputation monitoring.
- ClickFix Social Engineering: Accounting for 47% of initial access methods, this technique tricks users into pasting malicious commands into their systems, executing payloads directly into memory to evade detection.
- Cloud Shadow Activity: Attackers exploit cloud elasticity by deploying short-lived virtual machines (running for only 3–4 hours) and manipulating service quotas to scale attacks rapidly while leaving a minimal forensic footprint.
- Token Forgery and OAuth Abuse: Actors like Storm-0558 and Midnight Blizzard have successfully bypassed traditional MFA by forging authentication tokens or hijacking legacy OAuth applications to maintain persistence even after password resets.
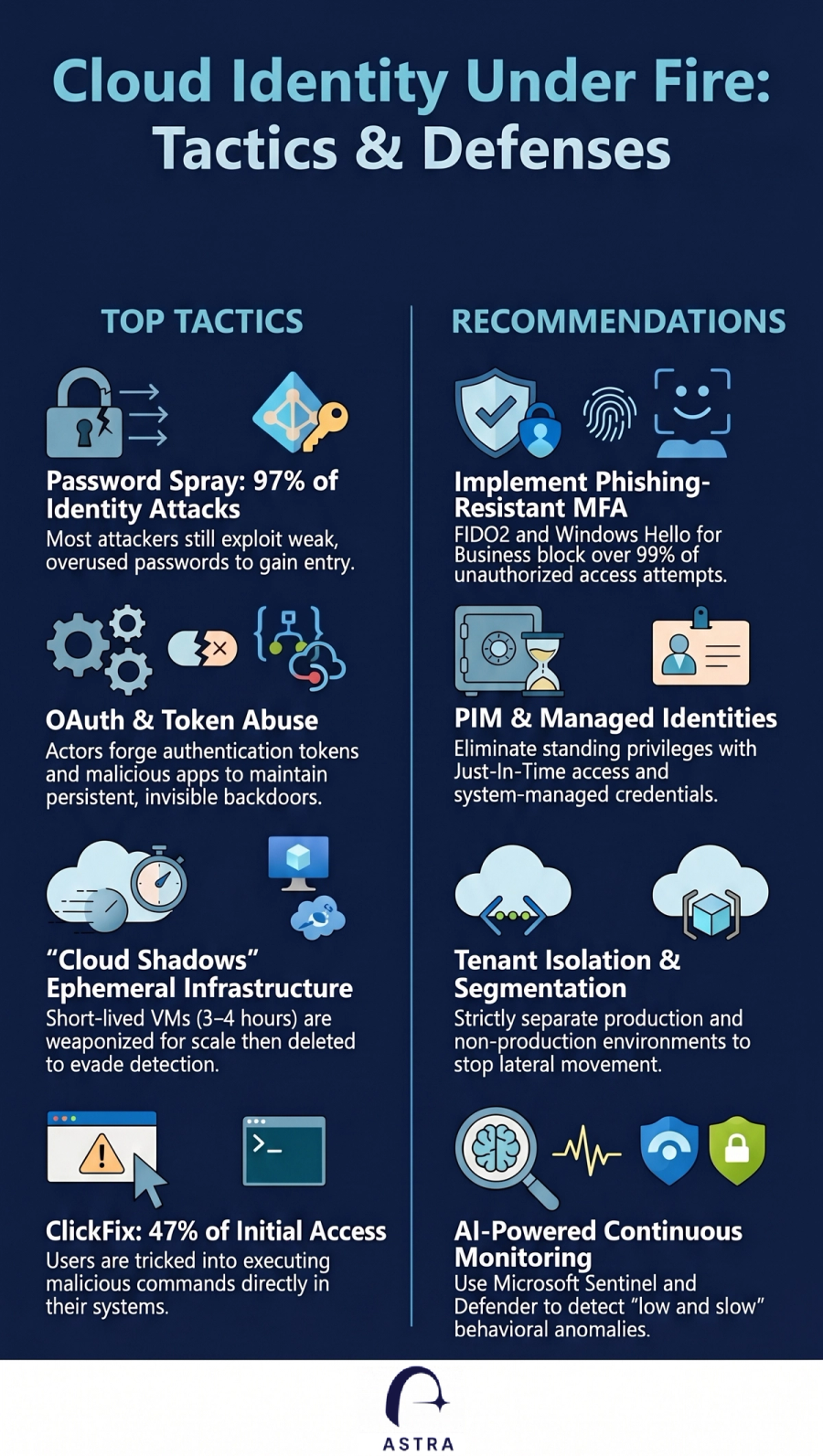
Key Recommendations for Azure Defense
To counter these evolving strategies, organizations should prioritize the following Azure-specific and identity-centric defenses:
- Enforce Phishing-Resistant MFA: Implement FIDO2 or Windows Hello for Business across all accounts. Traditional MFA is no longer enough; phishing-resistant methods block over 99% of unauthorized access attempts.
- Strict Identity Governance: Use Privileged Identity Management (PIM) to enforce just-in-time access and eliminate standing administrative privileges. Replace password-based credentials with Managed Identities to reduce theft risk.
- Tenant Isolation: Separate production and non-production (test) environments. This prevents attackers from using less-secure test accounts as springboards into critical production data.
- Continuous Monitoring: Integrate your monitoring solution with Azure to detect anomalous behaviors, such as rogue VM creation or rapid service quota consumption.
How Can Astra Help
Astra customers can use the built in use cases to identify any identities vulnerable to threat actors tactics and techniques.
Contact us for inquiries or a demo https://astrasec.io/#cta
